Crypto pockets Zerion revealed that North Korean-affiliated hackers used AI in a long-term social engineering assault to steal about $100,000 from the corporate’s sizzling wallets final week.
The Zerion crew released a autopsy on Wednesday, the place it confirmed that no person funds, Zerion apps or infrastructure have been affected and that it had proactively disabled the online app as a precaution.
Whereas the quantity was comparatively small in crypto hacking phrases, it’s one other incident of a crypto employee being focused for an “AI-enabled social engineering assault linked to a DPRK risk actor,” Zerion stated.
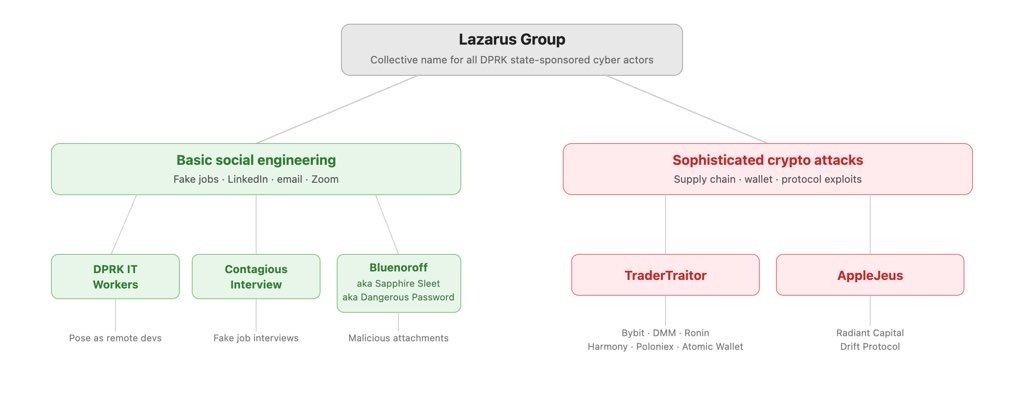
It’s the second assault of this nature this month, following the $280 million exploit of the Drift Protocol, which was the sufferer of a “structured intelligence operation” by DPRK-affiliated hackers. The human layer, not good contract bugs, has now develop into North Korea’s major level of entry into crypto corporations.
AI is altering the best way cyber threats work
Zerion stated the attacker gained entry to some crew members’ logged-in periods and credentialsin addition to private keys to firm sizzling wallets.
“This incident confirmed that AI is altering the best way cyber threats work,” the corporate stated.
It confirmed that the assault was comparable to people who had been investigated by the Safety Alliance (SEAL) final week.
Associated: Researchers discover malicious AI agent routers that can steal crypto
SEAL reported that it had tracked and blocked 164 domains linked to the DPRK group UNC1069 in a two-month window from February to April.
It said that the group operates “multiweek, low-pressure social engineering campaigns” throughout Telegram, LinkedIn and Slack. Malicious actors impersonate recognized contacts or credible manufacturers or leverage entry to beforehand compromised firm and particular person accounts.
“UNC1069’s social engineering methodology is outlined by endurance, precision, and the deliberate weaponization of present belief relationships.”
Google’s cybersecurity unit Mandiant detailed in February the group’s use of pretend Zoom conferences and a “recognized use of AI instruments by the risk actor for enhancing pictures or movies throughout the social engineering stage.”
DPRK’s social engineering is evolving
Earlier this month, MetaMask developer and safety researcher Taylor Monahan stated North Korean IT staff have been embedding themselves in crypto firms and decentralized finance initiatives for not less than seven years.
“The evolution of the DPRK’s social engineering methods, mixed with the rising availability of AI to refine and ideal these strategies, means the risk extends nicely past exchanges,” blockchain safety agency Elliptic stated in a weblog post earlier this 12 months.
“Particular person builders, mission contributors, and anybody with entry to cryptoasset infrastructure is a possible goal.”
Journal: How AI just dramatically sped up the quantum risk for Bitcoin

