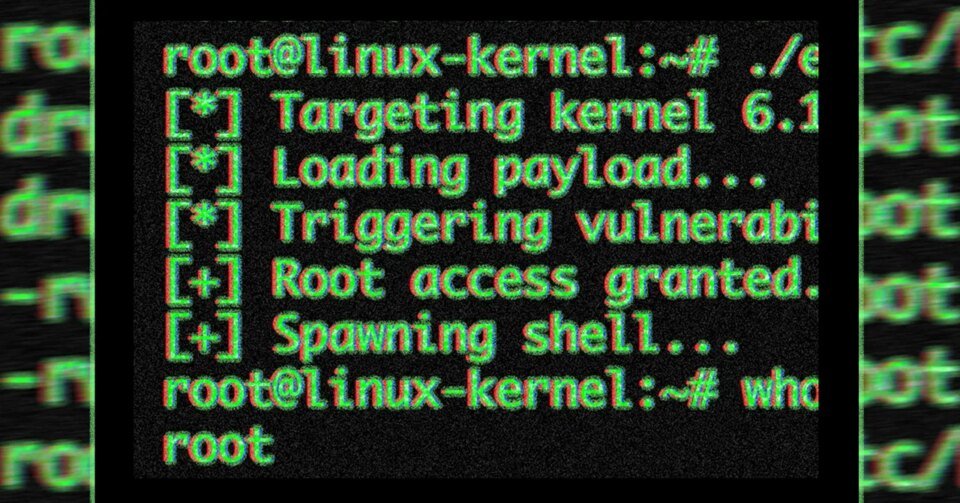
Publicly launched exploit code for an successfully unpatched vulnerability that offers root entry to nearly all releases of Linux is setting off alarm bells as defenders scramble to thrust back extreme compromises inside information facilities and on private gadgets.
The vulnerability and exploit code that exploits it had been released Wednesday evening by researchers from safety agency Theori, 5 weeks after privately disclosing it to the Linux kernel safety crew. The crew patched the vulnerability in variations 7.0, 6.19.12, 6.18.126.12.85, 6.6.137, 6.1.170, 5.15.204, and 5.10.254) however few of the Linux distributions had included these fixes on the time the exploit was launched.
A Single Script to Hack Them All
The important flaw, tracked as CVE-2026-31431 and the identify CopyFail, is a neighborhood privilege escalation, a vulnerability class that enables unprivileged customers to raise themselves to directors. CopyFail is especially extreme as a result of it may be exploited with a single piece of exploit code—launched in Wednesday’s disclosure—that works throughout all weak distributions with no modification. With that, an attacker can, amongst different issues, hack multi-tenant techniques, escape of containers primarily based on Kubernetes or different frameworks, and create malicious pull requests that pipe the exploit code by way of CI/CD work flows.
“‘Native privilege escalation’ sounds dry, so let me unpack it,” researcher Jorijn Schrijvershof wrote Thursday. “It means: An attacker who already has some solution to run code on the machine, at the same time as essentially the most boring unprivileged consumer, can promote themselves to root. From there they will learn each file, set up backdoors, watch each course of, and pivot to different techniques.”
Schrijvershof added that the identical Python script Theori launched works reliably for Ubuntu 22.04, Amazon Linux 2023, SUSE 15.6, and Debian 12. The researcher continued:
Why does that matter on shared infrastructure? As a result of “native” covers a variety of floor in 2026: each container on a shared Kubernetes node, each tenant on a shared internet hosting field, each CI/CD job that runs untrusted pull-request code, each WSL2 occasion on a Home windows laptop computer, each containerised AI agent given shell entry. All of them share one Linux kernel with their neighbors. A kernel LPE collapses that boundary.
The sensible menace chain appears to be like like this. An attacker exploits a recognized WordPress plugin vulnerability and will get shell entry as www-data. They run the copy.fail PoC. They’re now root on the host. Each different tenant is out of the blue reachable, in the way in which I walked by way of on this hack autopsy. The vulnerability doesn’t get the attacker onto the field; it adjustments what occurs within the subsequent ten seconds after they land there.
The vulnerability stems from a “straight-line” logic flaw within the kernel’s crypto API. Many exploits exploiting race conditions and reminiscence corruption flaws don’t persistently succeed throughout kernel variations or distributions, and typically even on the identical machine. As a result of the code launched for CopyFail exploits a logic flaw, “reliability isn’t probabilistic, and the identical script works throughout distributions, researchers from Bugcrowd wrote. “No race window, no kernel offset.”
CopyFail will get its identify as a result of the authencesn AEAD template course of (used for IPsec prolonged sequence numbers) doesn’t really copy information when it ought to. As a substitute, it “makes use of the caller’s vacation spot buffer as a scratch pad, scribbles 4 bytes previous the respectable output area, and by no means restores them,” Theori mentioned. “The ‘copy’ of the AAD ESN bytes ‘fails’ to remain contained in the vacation spot buffer.”
The Worst Linux Vulnerability in Years
Different safety specialists echoed the attitude that CopyFail poses a critical menace, with one saying it’s the “worst make-me-root vulnerabilities within the kernel in current occasions.”
The newest such Linux vulnerability was Dirty Pipe from 2022 and Dirty Cow in 2016. Each of these vulnerabilities had been actively exploited within the wild.